Threat intelligence and attack surface monitoring, tailored to your exposure.
[A]ctionable, [P]ersonalized,
[T]hreat Intelligence.
Threats.Report combines analyst review, exploit context, and external exposure analysis so your team can prioritize CVEs and remediation work with confidence.
You don't get more alerts. You get decisions.
Not Just Data. Intelligence.
Most platforms give you:
- Raw CVE feeds
- Generic threat alerts
- Port scan results
We deliver:
- CVE risk scoring based on real-world weaponization
- Business-specific prioritization
- External attack surface management and exposure mapping
- Industry-relevant threat actor monitoring
- CISO reporting and MSSP white-label threat intelligence deliverables
Built for security leaders who need to justify decisions and reduce risk, not chase dashboards.
Our Intelligence Methodology
We combine multiple authoritative data sources with expert analysis to produce intelligence that actually maps to your exposure.
Connect Your Assets
Add your domain and business details for tailored scanning
Automated Scanning
Our system continuously monitors for potential threats
Analysis & Reporting
Receive detailed reports with actionable insights
What You Receive
Each Threats.Report engagement includes a structured intelligence package designed for both technical teams and executive stakeholders.
Executive Risk Summary
Board-ready narrative of your current exposure posture
Exploit-Probability Ranked CVEs
Scored by real-world weaponization and your specific stack
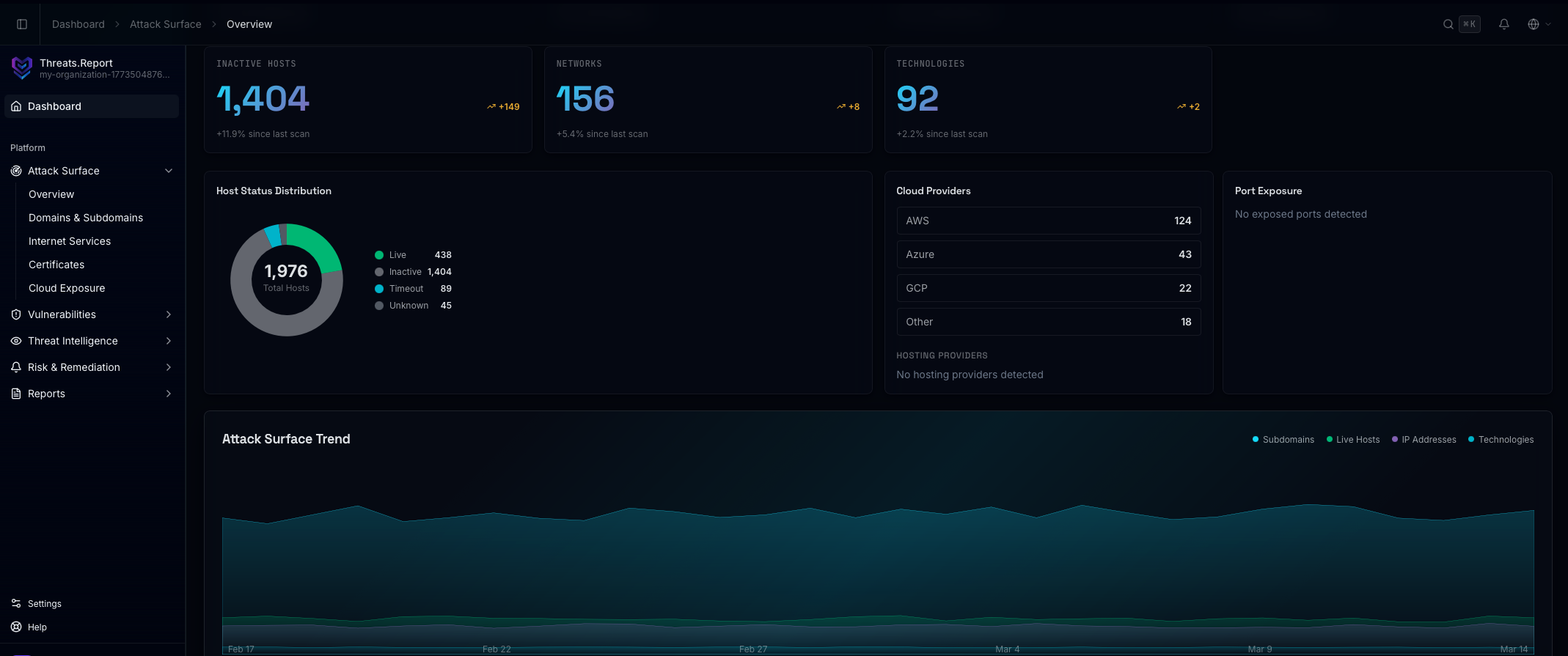
External Attack Surface Findings
Subdomains, services, misconfigurations, cloud exposure
Industry-Specific Threat Actor Trends
Who is targeting your sector and how
Actionable Mitigation Guidance
Concrete remediation steps tied to your context
Prioritized Remediation Roadmap
Sequenced by business risk, not CVSS score
Beyond CVEs:
Your Real Exposure
We continuously monitor your external footprint, not only your patching backlog.
Because attackers don't exploit "severity scores."
They exploit exposure.
Built for Serious Practitioners
MSSPs
Seeking premium client intelligence deliverables that differentiate your service offering and justify higher retainers.
Security Leaders
Preparing board-level reports and executive briefings that translate technical risk into business decisions.
Regulated Industries
Organizations operating in finance, healthcare, critical infrastructure, or government where compliance meets real threat exposure.
Public Infrastructure
Companies with significant public-facing infrastructure and external exposure that generic tools miss entirely.
Built by Security Researchers.
Threats.Report is developed by practitioners with hands-on experience across every layer of the modern threat landscape.
From the Blog
Featured Threat Intelligence Research
Fresh analysis from our threat research team to support security strategy, CISO reporting, and customer-facing MSSP narratives.
FAQs
Common Questions
Why should I trust analyst-curated intelligence over automated vulnerability scanners?
Unlike automated scanners that flood you with noise, threats.report delivers: • Analyst-curated intelligence — filtered for your specific tech stack and industry • Attack surface mapping — we identify your external exposure, not just known vulnerabilities • CVE prioritization — we rank by actual threat actor activity, not just CVSS score • Fix-first guidance — a clear, prioritized action list every reporting cycle
How do you prioritize CVEs when CVSS scores alone don't reflect real risk?
We don't rely on CVSS scores alone. Instead, we prioritize by: • Exploit maturity — whether a real public exploit exists • Threat actor activity — is this CVE actually being weaponized? • Stack relevance — does this vulnerability affect your technology? • Business context — how does this exposure impact your operations? A CVSS 9.8 with no exploit and no industry relevance ranks lower than a CVSS 7.2 being actively exploited against your sector.
What does external attack surface monitoring actually find that internal tools miss?
Internal tools scan what you tell them about. We find what you don't know about: • Forgotten subdomains and DNS records • Exposed cloud assets and storage buckets • Misconfigured services and open ports • Shadow IT and unauthorized infrastructure • Leaked credentials and third-party breaches Attackers enumerate your perimeter before attacking. We do it first.
How is this different from a generic threat feed I can get for free?
Free feeds dump raw data. We deliver actionable intelligence: • Raw feeds: thousands of IOCs with no context • threats.report: correlated threat TTPs tied to your stack • Raw feeds: vulnerability lists without prioritization • threats.report: CVEs ranked by exploit maturity and business impact • Raw feeds: data that sits unread in your SIEM • threats.report: prioritized actions your team can execute today
We're a small team with no dedicated SOC. Is this still relevant for us?
Perfect for lean teams. Without dedicated SOC headcount, you need: • Pre-triaged intelligence — not a firehose of raw alerts • Prioritized action items — ranked by business risk • Executive summaries — for board and client reporting • Context-driven guidance — not generic remediation steps We handle the analysis. Your team focuses on fixing what actually matters.